We often wonder whether Psychology and Neurology are same. The differentiation is also relevant as we travel from Privacy Rights to Neuro Rights.
The Current Privacy laws have touched the protection of Psychological manipulation of an individual for recognizing infringement of Privacy rights. The Indian data protection law (PDPB2019/DPA2021), lists “psychological manipulation which impairs the autonomy of the individual” as 0ne of the harms that lead to infringement of Privacy Rights.
As distinguished from this “Psychological manipulation” there could be “Neurological Manipulation” which will be part of the protection of neuro rights. For this purpose it is essential to distinguish Psychology from Neurology.
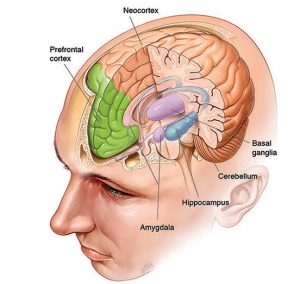
Neurology is a branch of medicine and devotes its attention to assessment and treatment of diseases of the nervous system. When a computer system is connected to the nervous system in such a manner as to read the nerve signals that transmit between the human central nervous system and the human body parts such as the muscles and organs, and perhaps manipulate the signals, we are dealing with a possible infringement of neuro rights of a person.
On the other hand, Psychology is a scientific study of the mind, behaviour and emotions of a person. When a computer system or information is used to alter the behaviour of a person or his emotions, or decisions, we can say that his privacy is being infringed.
The behaviour of a person is a reflection of the activity of neurons in his body. Hence psychological infringement can be caused by neurological infringement. Hence the two concepts of “Psychological intervention” and “Neurological intervention” are related.
If we take the example of a “Optical illusion”, the illusion leads the human to perceive an object different from what it truly is. But what something “Truly” is may itself be an illusion of a large number of persons.
When doctors use “Anaesthesia” they are only cheating the neural system to believe that there is no pain or sensation. Hence that person/part of the person which is anaesthetised is unable to feel the heat, cold or pain though the object he touches may really hot as per the accepted standards. This is a neurological intervention.
On the other hand, if a person is “hypnotized” and through hypnotic suggestions is made to believe that the object is not hot or he does not feel the pain, he may actually donot recognize the heat or pain. In this case, the psychological manipulation is so strong that it induces the neurological changes which otherwise may directly be achieved by an anaesthesia.
This example shows that neurological changes can be brought in by psychological suggestions provided the suggestions are strong enough. This phenomenon has been proved in the “Hypnotic state” where the sub conscious mind of a person is being spoken to by the hypnotist.
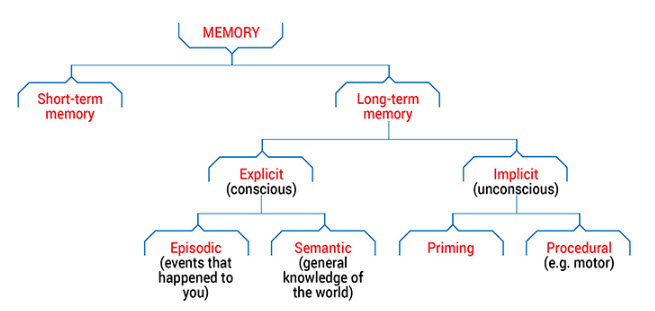
In the normal conscious state, the human mind works under its legacy memory and the pre-programmed active nervous system and hence it will feel the heat or pain despite oral suggestions from others. Perhaps some of the “Cult Leaders” have the capability of hypnotic control on persons who appear to be fully awake and in such persons the belief system is strong enough to take them to a hypnotic trance if the cult leader speaks to them.
Thus we can conclude that psychological manipulations can be converted into neurological manipulations and vice versa.
When we try to regulate “Privacy Rights” therefore we need to understand that at the peripheral level, the regulations affect “Privacy” in the “Psychological Domain”. When we try to dive deeper, we come to the neurological domain and need to look at neuro rights.
To explain this two levels that separate the Privacy rights and Neuro Rights, we can take the example of Data which exists in multiple states.
For example let us take identified personal data and anonymised personal data. One law may address identified personal data and another may address anonymised personal data. There is a layer of separation between identified personal data and anonymised personal data which is the anonymisation technology. If this technology is weak, we can say that there is no difference between anonymised data and identified data and privacy can be infringed if either of the data is available in wrong hands. In that case we need one law to take care of privacy infringement of both identified and anonymised data.
But if technology is “reasonably” strong, it is possible to keep the two regulations separate.
Similar argument can be made on “Un encrypted and Encrypted Data”. If the encryption is strong, there can be one law for unencrypted law and another for Encrypted data”. Otherwise we need a common law.
When there is a reasonably strong security that separates one set of objects and the other and law is made differently with the confidence that conversion one set of object to the other is technically infeasible, then forced conversion should be considered as a “Malicious activity or a Crime”.
Indian data protection law has done this by a specific provision in PDPB 2019/DPA 2021 which criminalizes re-identification of de-identified information without authority. (also applies to de-anonymisation of anonymised data).
Similarly, when we consider a legal provision for Neuro rights different from Privacy Rights, we need to place a strong barrier in between what is considered as the psychological domain and the Neurological domain.
This will be one of the biggest challenges in conceptualizing the Neuro Rights law and defining its applicability.
In the Data Protection laws, we define applicability from “Presence of a processing company in a given jurisdiction” and “Data being collected from within the jurisdiction” as well as “data related to doing business from a different country or profiling the persons in one country from another country”.
If we use this analogy, we can define psychological intervention in such a manner that it extends to direct or indirect neurological interventions or vice versa.
This is an area for debate by the law makers.
To summarize, here we have discussed the presence of two concepts namely “Psychology” and “Neurology” from the Personal data and Neuro data perspectives and how they may be inter related.
(Debate will continue…)
Naavi

 the brain is from the sensory organizations. Data Output is mainly to the different motor organizations. If therefore there is a heat sensation, brain may instruct the relevant muscles to move the body away from the heat.
the brain is from the sensory organizations. Data Output is mainly to the different motor organizations. If therefore there is a heat sensation, brain may instruct the relevant muscles to move the body away from the heat.